Dynamic Data Maps
Build complete data maps without questionnaires
Fully automate data maps for all processing activities with modern solutions to scan code, websites, mobile apps, 3rd party apps, contracts, and documentation. Eliminate all manual assessments. Utilize AI agents to fill in any gaps.


Trusted by privacy leaders at
Accurately map data flows with real-time scanning
Utilize AI agents to fill in any blind spots
Eliminate all manual assessments
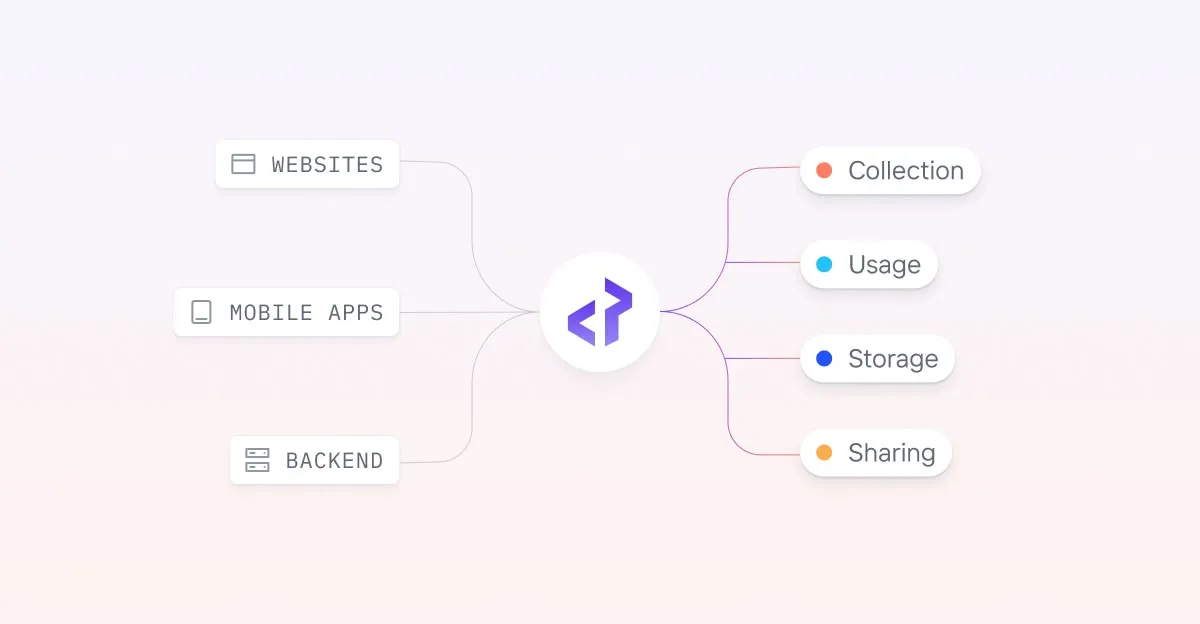
Technology
Data mapping automation for all data sources

Get full data visibility and eliminate manual assessments
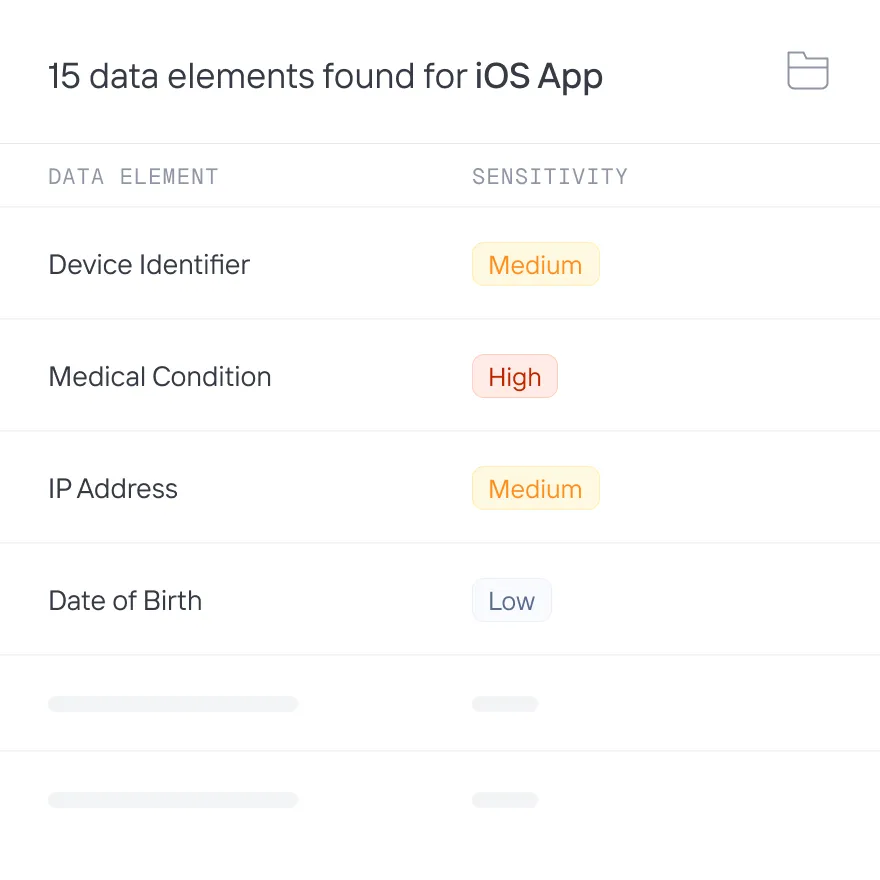
Data Inventory
Identify all personal data elements
Build a complete inventory of all personal data across processing activities. Auto-categorize data, tagging sensitive health, financial, and location data. Quickly validate findings with each instance of data processing linked to the data source.
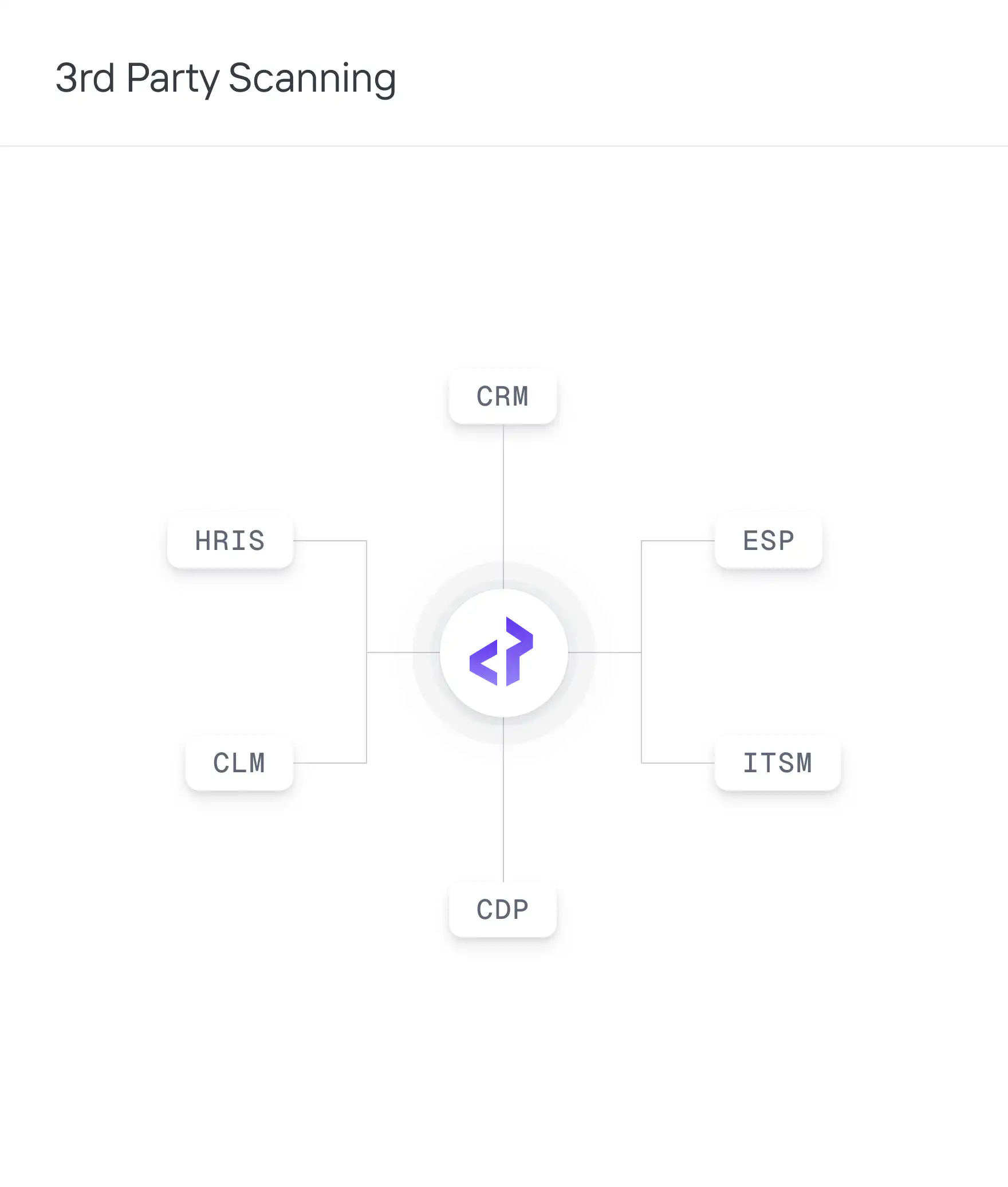
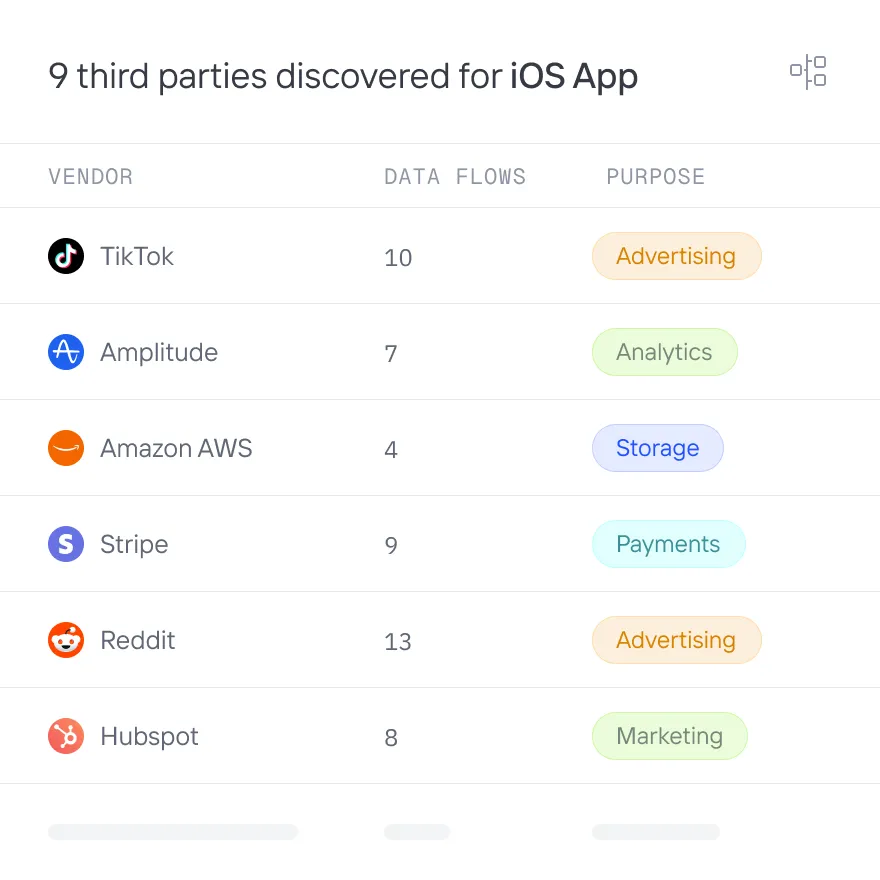
Third Party inventory
Discover all third parties
Identify all third parties receiving personal data. Obtain full backend data sharing coverage by scanning 3rd party apps such as tag managers and customer data platforms. Get real-time alerts for each new third party or data element shared.
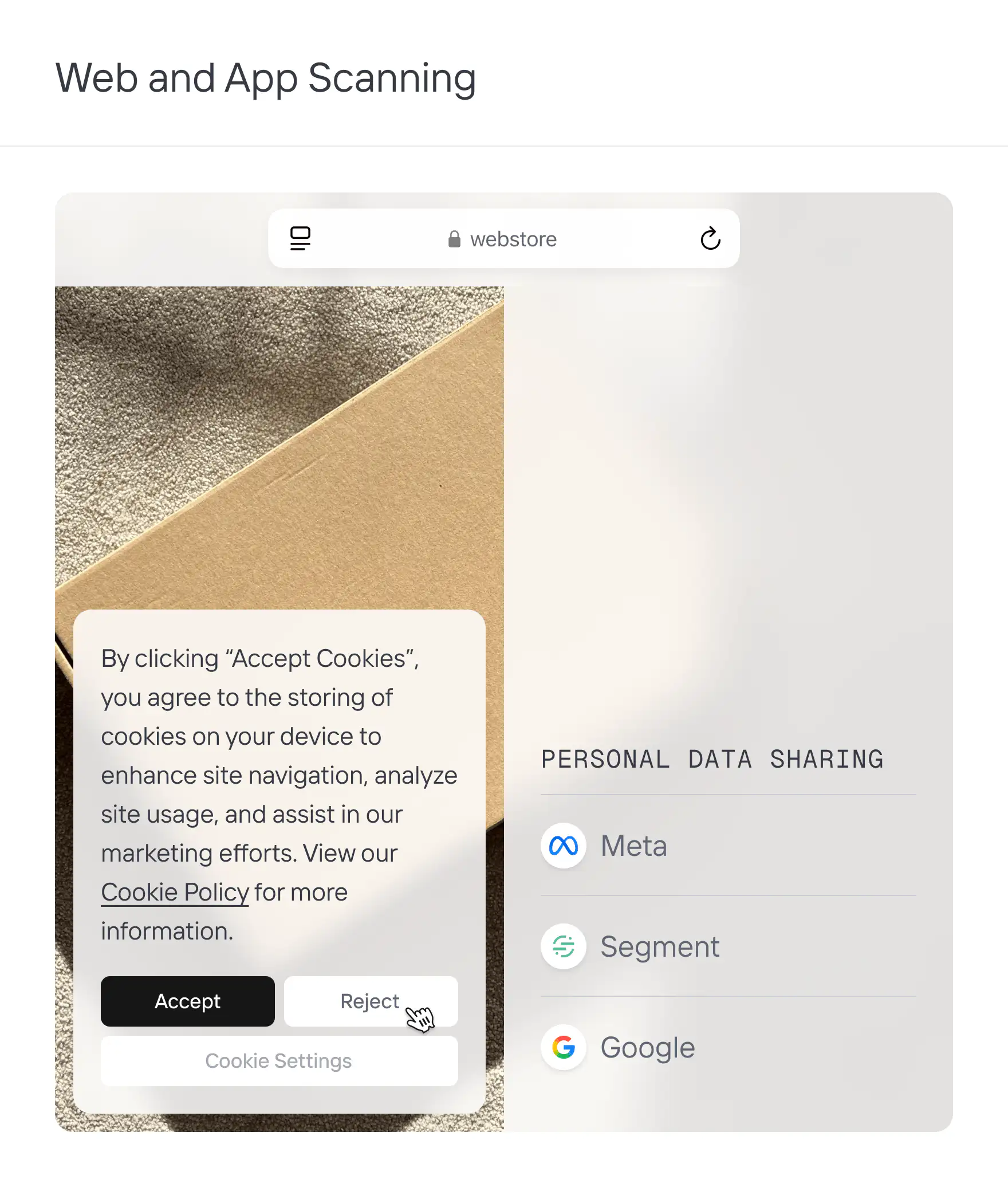
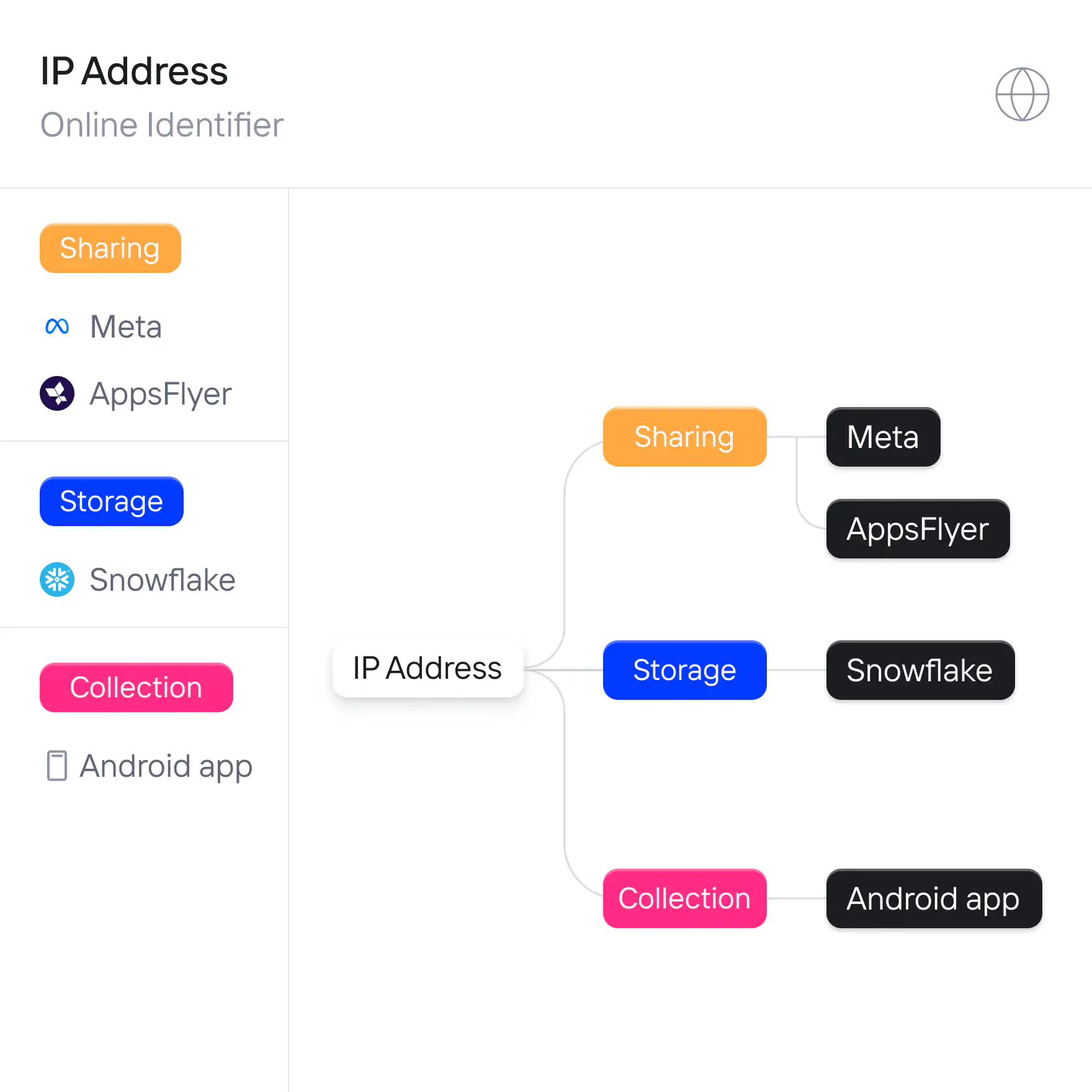
Data Flows
Map all data flows
Track each data element moving through your websites, apps, databases, backend software, and third parties. Monitor data shared across borders and with AI applications. Generate diagrams showing how data is collected, stored, and shared via forms, APIs, SDKs, pixels, tag managers, CDPs, SaaS apps, etc.
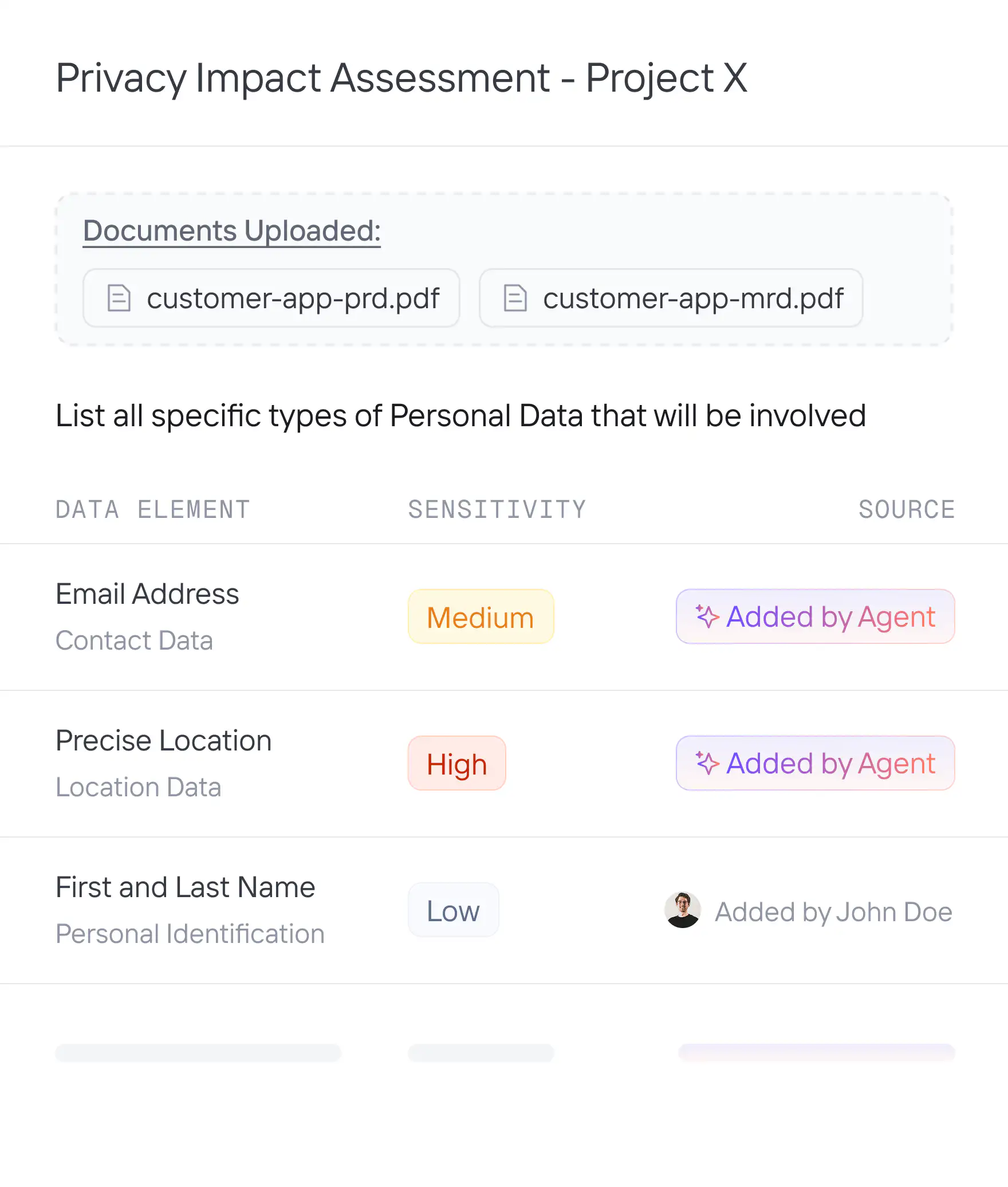
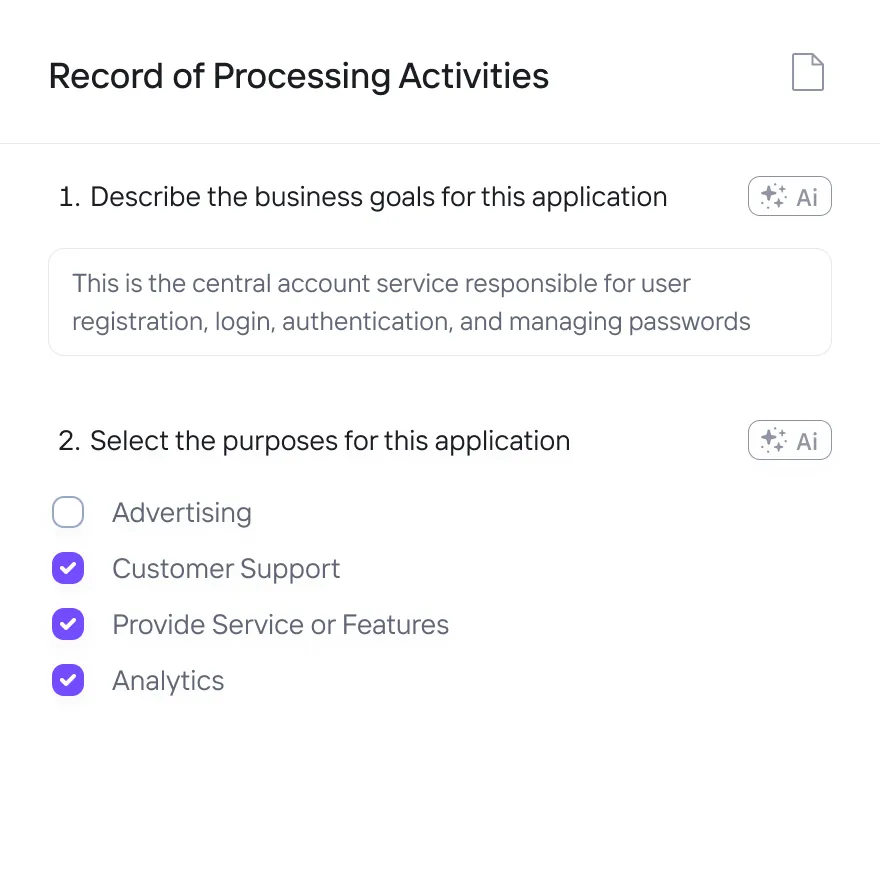
ropa automation
Populate 100% of RoPAs with AI agents
Utilize AI agents to complete entire RoPAs by pulling information from real-time scanning and analyzing any relevant documentation. Automatically document how personal data is collected, used, stored, and shared. Eliminate manual input and delays from stakeholders.
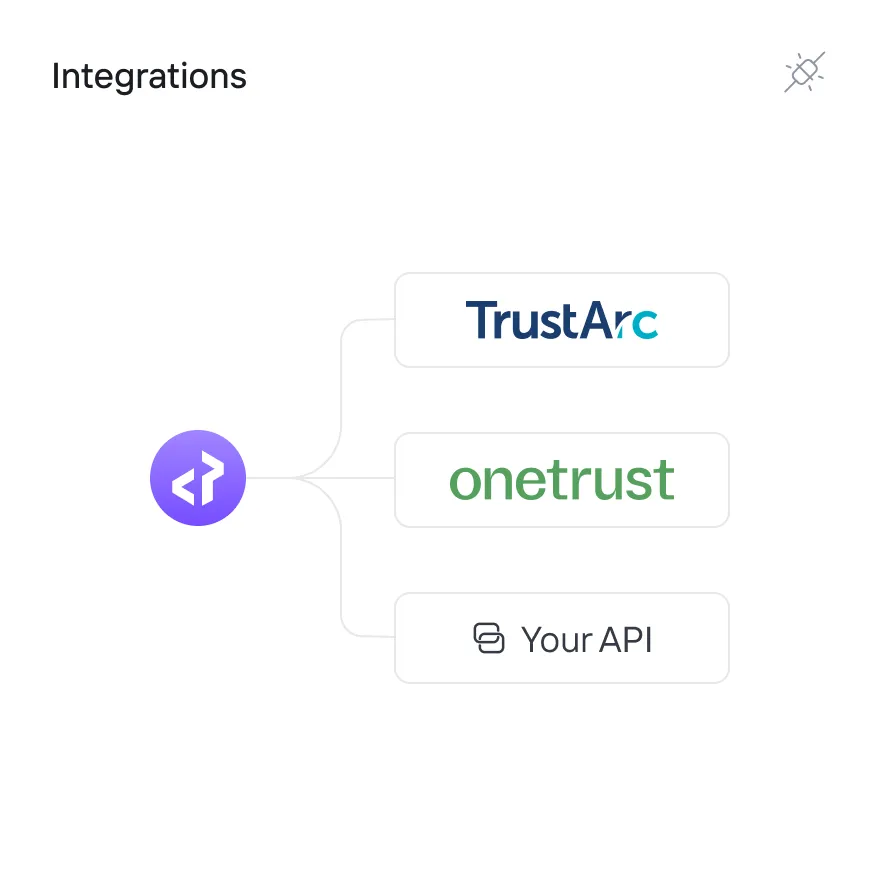
Integrations
Sync to OneTrust and other privacy tools
Centrally build and manage data maps in Privado AI or other privacy tools like OneTrust or TrustArc. Sync all data mapping details to other tools with accurate, up-to-date information from Privado AI. Save your teams months of manual data mapping.
“Privado AI enables us to uphold the highest standards of data privacy. By providing comprehensive data visibility, our privacy team can better understand what data we have, where it's located, and how it's shared -- without taking time away from our engineering and product teams.”